Introduction: Why SCADA Protection Matters
If you’ve ever dealt with SCADA protection issues on the plant floor, you know how frustrating they can be. I remember a time when a minor oversight in security almost brought production to a halt. SCADA systems are the backbone of industrial automation, managing everything from controlling machinery to monitoring critical infrastructure. Without them, our factories would be in chaos.
However, these systems aren’t foolproof. Their connectivity, which is a strength, also makes them vulnerable. Outdated software, unsecured networks, and weak access controls are just a few examples of where things can go wrong. The stakes are high, and breaches can lead to significant downtime, financial loss, and even safety hazards.
That’s why robust SCADA protection measures are non-negotiable. You want to ensure that your system is not only efficient but also secure against both external and internal threats. We’ll dig into practical strategies that will help you safeguard your SCADA systems effectively.
Understanding SCADA System Vulnerabilities
Common Vulnerabilities in SCADA Systems
SCADA systems, by their nature, often run on older software platforms that haven’t been updated in years. This makes them prime targets for cyber threats. Additionally, many of these systems operate on unsecured networks. I once spent an entire weekend fixing vulnerabilities that arose because a SCADA system was directly connected to the internet without any security measures.
Moreover, SCADA systems often lack encryption for data in transit. This oversight makes it easier for hackers to intercept critical information. And don’t forget about physical vulnerabilities—access to SCADA control rooms is sometimes easier than accessing your office pantry.
Impact of Cyber Threats on SCADA
Cyber threats can cause severe disruptions. Imagine your operations grinding to a halt because of a ransomware attack that locks you out of your own systems. That’s a nightmare scenario that no engineer wants to face. Unfortunately, I’ve seen it happen. An acquaintance at another plant dealt with a breach where hackers accessed the system and changed operational parameters, resulting in costly downtime.
Pro Tip: Never underestimate the power of regular software updates. They patch vulnerabilities that hackers love to exploit.
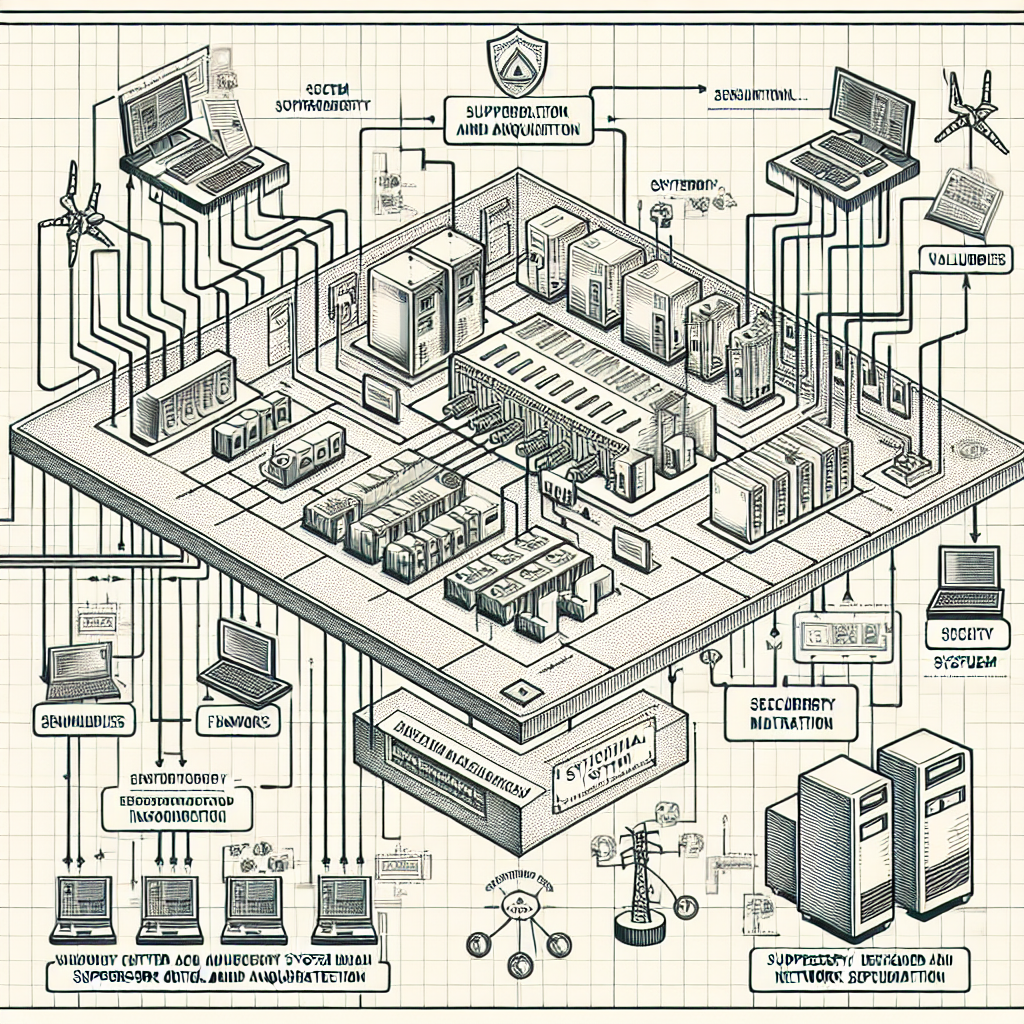
Building a Secure SCADA Network
Physical Security Measures
First off, don’t ignore physical security. Your SCADA hardware should be in a secure location, inaccessible to unauthorized personnel. I’ve seen cases where someone accidentally knocked over a server rack, causing a system outage. Lock those panels and control rooms, and use surveillance cameras where necessary.
Additionally, consider implementing biometric access controls. While it might sound like overkill, these measures significantly reduce the chance of unauthorized physical access. In my experience, securing the physical space is often overlooked, yet it’s your first line of defense.
Network Segmentation and Firewalls
Network segmentation is a lifesaver. By dividing your network into smaller, isolated segments, you can limit the spread of an attack. Moreover, firewalls act as gatekeepers, preventing unauthorized access. Make sure your firewall rules are up to date and tailored to your specific needs. In my experience, setting up a Demilitarized Zone (DMZ) for public-facing services can also add an extra layer of security.
Here’s a table comparing firewall options:
| Firewall Model | Best For | Key Features |
|---|---|---|
| Cisco ASA 5500-X | Large Enterprises | Advanced threat protection, VPN support |
| Fortinet FortiGate 60E | Small to Medium Businesses | Easy-to-configure, cost-effective |
| Palo Alto Networks PA-220 | Remote Offices | Application-aware, high throughput |
From my experience: A well-configured firewall can mean the difference between a minor inconvenience and a major crisis.
Regular Security Audits
Regular security audits are crucial. They help you identify and fix vulnerabilities before they become problems. I personally prefer conducting these audits quarterly. You’d be surprised what you can catch—a misconfigured router, outdated firmware, or even unauthorized devices connected to your network.
Furthermore, involve third-party experts for an external audit occasionally. Fresh eyes can spot issues you might overlook. Remember, the goal is to stay ahead of potential threats. Consistent checks and updates keep your SCADA systems resilient.
Implementing Strong Authentication and Access Controls
Two-Factor Authentication
Let’s talk about two-factor authentication (2FA). It’s not just for your email account but is crucial for SCADA systems too. By requiring something you know (a password) and something you have (a mobile device), 2FA makes unauthorized access much harder. I can’t stress enough how effective this is in providing an extra security layer.
Moreover, setting up 2FA is relatively simple but incredibly effective. It’s like adding an extra lock on your front door. In my opinion, it’s a no-brainer for any SCADA setup.
Role-Based Access Control
Role-Based Access Control (RBAC) is another strategy you can’t ignore. It ensures users have access only to the resources necessary for their role. Implement this to limit the risk of unauthorized access. I’ve seen situations where someone with unnecessary access rights accidentally altered crucial settings. That’s a headache you don’t want.
Here’s the thing: with proper RBAC, you can prevent such mishaps. Set permissions based on roles and responsibilities. This minimizes the chances of human error. Keep your access controls updated; people’s roles change, and so should their access rights.
To wrap up this section, remember that securing a SCADA system isn’t just about technology but also about implementing strong policies and procedures. Each layer of security you add reduces the risk of a breach.
Regular Software Updates and Patch Management
Keeping your SCADA systems updated is like making sure your car doesn’t run out of oil. It’s crucial for smooth operations. Now, I know updates can feel like a nuisance, especially when they pop up during critical times, but trust me, they’re your first line of defense against vulnerabilities. Regular software updates and patch management aren’t just tech buzzwords—they’re essential for SCADA protection.
Automated Patch Deployment
Here’s the thing: manually updating software is a pain. It takes time and leaves room for human error. Automated patch deployment, on the other hand, streamlines the process. It ensures updates are applied consistently and efficiently. Systems like Microsoft’s Windows Server Update Services (WSUS) or third-party solutions can manage this for you. Moreover, they can be scheduled to run during non-production hours to minimize disruptions. You can’t afford to let a critical patch go uninstalled because someone forgot to hit “install.”
Vendor Collaboration
Now, don’t underestimate the power of working closely with your vendors. They’re the ones developing these systems, after all. Regularly communicate with them to stay informed about new patches and updates. They often provide valuable resources and alerts for security patches specific to your SCADA systems. I remember a time when we missed a critical update from a vendor. It led to a vulnerability that could’ve been avoided. Since then, maintaining an open line with vendors has been non-negotiable for me.

Training and Awareness for SCADA Operators
SCADA systems are only as secure as the people operating them. If your operators aren’t trained on security protocols, you’re leaving a door wide open. Regular training programs are vital to ensure everyone knows the ropes. They need to understand both routine tasks and emergency procedures.
Regular Training Programs
In my experience, training isn’t a one-and-done deal. You can’t expect operators to handle updates, recognize phishing attempts, or manage unexpected alarms effectively without ongoing education. It’s like teaching someone to drive and then never letting them practice. Keep the sessions interactive and up-to-date with the latest threats and best practices.
Incident Response Drills
Incident response drills prepare your team for the unexpected. Think of these like fire drills, but for cyber threats. Running these drills regularly helps teams react swiftly and correctly when real incidents occur. I once witnessed a team flawlessly execute a response plan during a cyber attack simulation. This wasn’t luck—it was practice. Their rapid, coordinated response minimized downtime and saved the company from a potential data breach.
Monitoring and Incident Response Strategies
Even with all precautions, things can go sideways. That’s why real-time monitoring and a solid incident response plan are vital for effective SCADA protection.
Real-Time Monitoring Tools
Real-time monitoring tools are like your SCADA system’s eyes and ears. They detect anomalies and potential threats as they happen. Tools like Siemens’ SIMATIC PCS 7 or Rockwell’s FactoryTalk can provide real-time insights into your system’s health. Furthermore, integrating these tools with your network allows for immediate alerts when something’s amiss. This proactive approach can prevent small issues from snowballing into major incidents.
Establishing an Incident Response Plan
A well-crafted incident response plan is your safety net. It outlines clear steps for identifying, containing, and eradicating threats. Include roles and responsibilities for each team member, communication protocols, and recovery procedures. A good plan also has a post-incident review to learn from the event and prevent future occurrences. And remember, the quicker you can recover, the less impact an incident will have on your operations.
Common Mistakes to Avoid
Even seasoned engineers can slip up. Here are some common mistakes I’ve seen:
- Ignoring Software Updates: It’s easy to delay updates, but doing so leaves systems vulnerable. Schedule them during off-peak hours and automate where possible.
- Weak Password Policies: If passwords are easy to guess, your system is at risk. Use complex passwords and change them regularly. Implement 2FA to add an extra layer of security.
- Overlooking Physical Security: Don’t underestimate the importance of securing the physical premises. Locked doors and restricted access areas are basic but effective.
- Insufficient Training: Assume your team is prepared, and you’re asking for trouble. Continuous education is crucial for preparedness.
- Inadequate Monitoring: Without real-time monitoring, you’re flying blind. Invest in tools that alert you to issues as they arise.
Frequently Asked Questions
What are the most common SCADA vulnerabilities?
The most common SCADA vulnerabilities include outdated software, weak authentication mechanisms, and unsecured network configurations. Malware and phishing attacks also exploit these weaknesses, making regular updates and strong security protocols essential.
How often should SCADA systems be audited for security?
SCADA systems should be audited for security at least annually, but more frequent audits are recommended as new threats emerge. Quarterly assessments can help identify vulnerabilities before they are exploited.
What are the best practices for SCADA software updates?
Best practices include automating patch deployments, scheduling updates during off-peak hours, and collaborating with vendors to stay informed about critical patches. It’s also important to test updates in a controlled environment before live deployment.
How can we improve SCADA operator training?
Improving operator training involves regular, interactive training sessions, real-world scenario drills, and incorporating feedback from past incidents. Keeping training materials current with evolving threats is also crucial.
How should we handle SCADA incidents when they occur?
Act quickly. The first step is containment to prevent further damage. Follow your incident response plan, communicate effectively, and conduct a post-incident review to improve future responses.
Key Takeaways for SCADA Security
SCADA protection isn’t a one-size-fits-all solution. A multi-layered approach is the best way to safeguard your systems. Regular updates, comprehensive training, and vigilant monitoring form the foundation of a secure SCADA environment. However, don’t wait for something to go wrong before taking action.
Proactive measures like automating updates, conducting regular training programs, and developing a robust incident response plan are critical. By implementing these strategies, you can significantly reduce the risk of security breaches and ensure your SCADA systems run smoothly.
So, what’s stopping you? Start fortifying your SCADA systems today and sleep easier knowing you’re prepared for whatever comes your way.
Here’s one last tip: Document everything. Logs and records can be your best friends during a security audit or incident investigation.

I am an electrical & automation engineer with extensive experience in Design, PLC programming, SCADA development, and IoT integration. I have a strong background in the industry, focusing on the Design & Development of Hardware, Software &Industry 4.0 technologies, and the integration of intelligent manufacturing systems.
I have a deep understanding of electrical principles and am proficient in various programming languages, including Ladder Logic, Structured Text, and Python. In addition, I have experience with various PLC, SCADA & IoT technologies and a track record of successful integration projects for various clients.

