Introduction: Why SCADA Security Matters
If you’ve ever dealt with SCADA security issues on the plant floor, you know how frustrating they can be. I’ll never forget the time a virus wormed its way into one of our SCADA systems and knocked out an entire production line for nearly eight hours. Talk about a nightmare!
Recent incidents have shown us just how vulnerable these systems can be. In one case, a manufacturing plant lost millions when a cyber attack targeted their SCADA network and wreaked havoc on their production schedules. The impact of such breaches isn’t just financial; it can also damage reputations and erode client trust.
So, what’s the takeaway here? The importance of a proactive security strategy for SCADA systems can’t be overstated. Whether it’s safeguarding against external cyber threats or protecting against internal mishaps, taking action before a breach occurs is crucial. Trust me, the peace of mind you’ll gain is worth the effort.
Understanding SCADA Systems
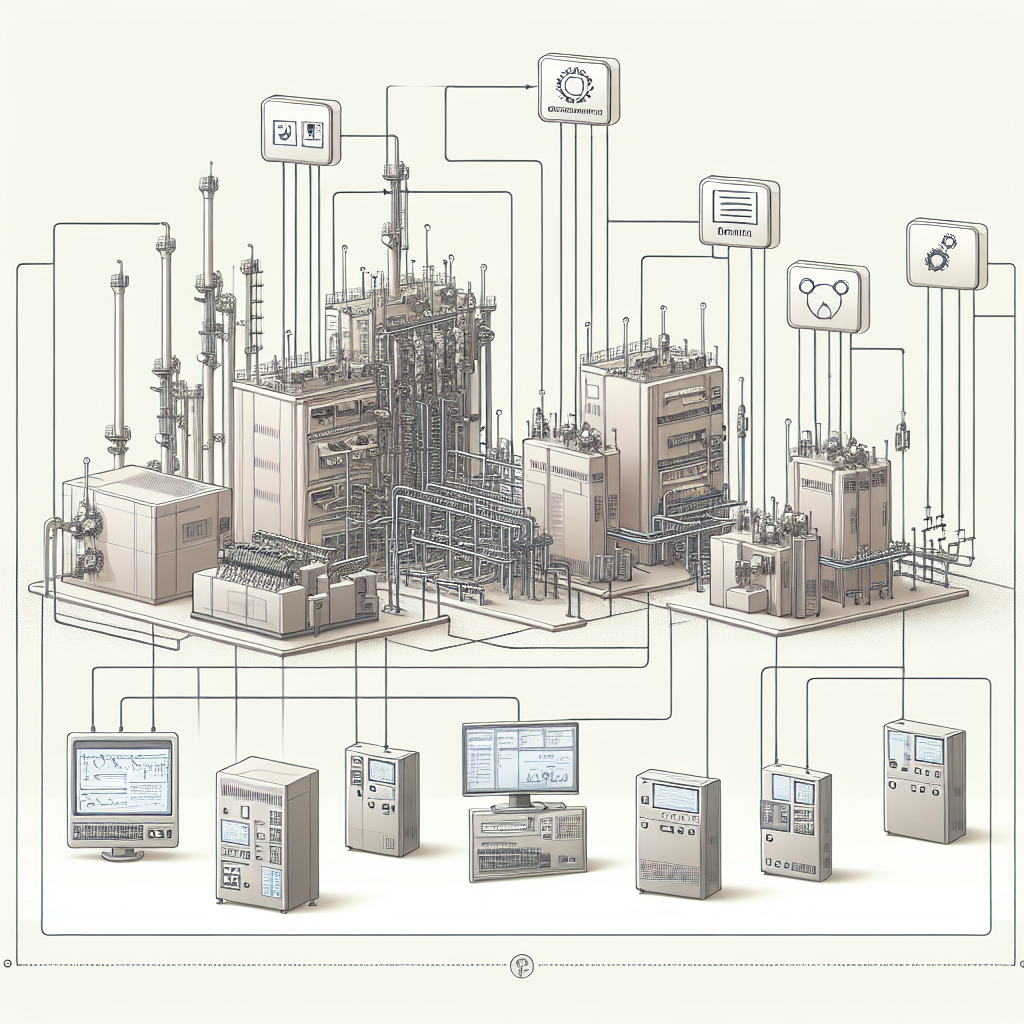
Now, let’s get into the nuts and bolts of SCADA systems. These setups aren’t just a single entity but a combination of multiple components that work together to monitor and control industrial processes. Think of them as the nervous system of your plant.
Components of SCADA
At the heart of a SCADA system are its components: PLCs (Programmable Logic Controllers), RTUs (Remote Terminal Units), and HMIs (Human-Machine Interfaces). PLCs are like the brain, executing control actions based on the real-time data they receive. RTUs act as intermediaries, gathering data from various sensors and sending it back for processing. HMIs, on the other hand, provide the user interface, allowing operators to monitor and interact with the system.
Common Communication Protocols
For communication, SCADA systems rely on protocols like Profinet, Modbus, and Ethernet. Profinet is popular for its speed and flexibility in industrial environments. Modbus is often used for connecting industrial devices due to its simplicity. Ethernet ties it all together, enabling high-speed data transfer across the network.
Identifying Security Risks in SCADA
Let’s talk about the boogeymen lurking in the dark corners of your SCADA systems: security risks. Common vulnerabilities like open ports and default passwords are an invitation for trouble. In my experience, these are the low-hanging fruits for attackers looking to breach your network.
Common Vulnerabilities
Things like unsecured access points and outdated software can turn your SCADA system into a sitting duck. I’ve seen engineers overlook basic software updates — a small oversight that can lead to big problems. Ensuring that these common entry points are secured is your first line of defense.
Cyber Threat Landscape
The cyber threat landscape is constantly evolving, making it imperative to be on your toes. Ransomware attacks on SCADA systems are on the rise, and they can bring businesses to a standstill. These aren’t just hypothetical scenarios but real threats that have taken down major operations.
Moreover, don’t underestimate the risk of insider threats and physical security lapses. Not every threat is digital. Sometimes it’s the disgruntled employee who knows the system inside out.
Implementing Robust Security Measures
So, how do you keep the wolves at bay? By implementing robust security measures, of course. The real trick is to shield your SCADA systems without hampering operational efficiency.
Network Segmentation
Here’s the thing: you need to isolate your SCADA systems from other networks. Network segmentation is a game-changer when it comes to SCADA security. By creating separate zones within your network, you limit the spread of any possible intrusion. Think of it as putting up firewalls inside your firewall.
Access Control
When it comes to access control, enforce stringent user authentication practices. Don’t just hand out access like candy. Instead, use role-based access controls to ensure each user only gets the permissions they absolutely need. It’s a bit like giving keys only to rooms people need to enter.
Pro Tip: Use multi-factor authentication (MFA) to add an extra layer of security. It might seem like a hassle, but it significantly reduces unauthorized access.
Regular Audits
Finally, regular security audits and software updates are non-negotiable. I’ve been on too many sites where outdated software was the Achilles’ heel. Audits help identify vulnerabilities before they become a problem. Schedule them routinely, and you’ll catch issues early.
Additionally, keep an eye on security patches from your equipment vendors. For instance, Siemens and Rockwell frequently release patches that address newly discovered vulnerabilities. Staying updated is a critical part of your security strategy.

By following these measures, you can ensure your SCADA systems are as secure as possible. Remember, it’s always better to be proactive when it comes to security.
Using Firewalls and Intrusion Detection Systems
Alright, firewalls. Think of them as bouncers at a club, only letting the right folks in. When it comes to SCADA security, firewalls are your first line of defense. They control the flow of data between your SCADA network and the outside world. You set the rules — what’s allowed, what’s not. In my experience, you’ll want to create strict rules for traffic. Only allow what you absolutely need.
Now, intrusion detection systems (IDS) are like security cameras. They don’t stop intrusions, but they alert you when something’s off. IDS can be really beneficial in detecting anomalies. For instance, if there’s unusual traffic at odd hours, you’ll know something’s up. When configuring these systems, regularly update the signatures and rules. And, integrate them with your firewalls for a more robust defense.
Here’s the thing: effective configuration is everything. Use both whitelist and blacklist approaches. Moreover, conduct frequent audits to tweak these systems. In my experience, a firewall without regular updates is as good as none. Trust me on this, you don’t want to find out they’re outdated in the middle of a breach.
Training and Awareness for Personnel
Technical measures are great, but if your staff isn’t on the same page, they’re not much help. Training your team on security protocols is crucial. I’ve seen too many breaches due to simple human errors. Regular training sessions can ensure everyone knows how to handle security risks.
Developing a security-conscious culture means everyone from top management to the plant floor worker understands the importance of SCADA security. Encourage them to report suspicious activities. Furthermore, keep them updated on emerging threats. Organize workshops or seminars, if possible, to keep security top of mind.
In my experience, a team that’s aware is a team that’s prepared. Regular updates and open communication channels can make a significant difference. The real trick is making security a part of your daily operations, not just an afterthought.
Common Mistakes to Avoid
Even the best of us can slip up. Here are some common mistakes to avoid when securing SCADA systems.
1. Ignoring Software Updates
I once worked at a plant where a critical patch for the SCADA software was ignored for months. Eventually, a known vulnerability was exploited, causing a major upset. Always stay on top of updates from your software vendors.
2. Overlooking Physical Security
It’s easy to focus on digital threats, but don’t forget the physical ones. I remember a case where someone gained unauthorized access to a control room because they “looked official.” Secure all access points and know exactly who can get to your sensitive areas.
3. Using Default Passwords
I’ve lost count of how many times I’ve seen systems still using the default “admin/admin” login. Change all default passwords immediately upon installation and use complex, unique passwords for each system.
4. Failing to Segment Networks
Network segmentation is crucial. Without it, an attacker who breaches one part of your system could potentially access everything. Create distinct zones for different parts of your plant’s operations.
5. Not Conducting Regular Audits
Don’t wait for a breach to show you your weaknesses. Regular audits can catch vulnerabilities before they become problems. It’s worth the time and effort to schedule these regularly.
Future Trends in SCADA Security
Let’s talk future. AI is making waves in SCADA security. Imagine predictive algorithms that can anticipate threats before they happen. It’s not sci-fi; it’s happening. AI can analyze vast amounts of data to identify patterns and predict intrusions.
Blockchain is another buzzword. Its decentralized nature offers more secure transactions. While it’s still emerging in industrial settings, its potential for securing SCADA systems is promising. For instance, blockchain can ensure that data hasn’t been tampered with during transactions.
As for future threats, IoT is a double-edged sword. More devices mean more entry points for attackers. Consequently, you’ll need to stay ahead with new solutions. Honestly, I think the future will bring more sophisticated threats, but also smarter solutions. Stay informed, adapt, and you’ll be on the safer side.
Frequently Asked Questions
What are the most common SCADA vulnerabilities?
Common vulnerabilities include weak passwords, unpatched software, and unsecured remote access points. In my experience, these are often overlooked but can be easily fixed with routine checks and updates.
How often should security audits be conducted?
I recommend audits at least once a year. However, if you’re in a high-risk industry, consider semi-annual checks. Audits help identify gaps and ensure your measures are up to date.
What are the steps in securing remote access?
First, use VPNs for secure connections. Secondly, enforce multi-factor authentication. Lastly, monitor remote sessions actively. In my experience, these steps greatly reduce the risk of unauthorized access.
Which protocols are most secure for SCADA communication?
Protocols like DNP3 Secure and IEC 60870-5-104 with security extensions are preferred. They offer added layers of security compared to older protocols.
How can small plants afford SCADA security?
Start with the basics: strong passwords, firewalls, and regular employee training. Additionally, consider cloud-based security services, which can be more cost-effective.
How do I handle insider threats?
Implement strict access controls and monitor employee activities. Regular audits and having a whistleblower policy in place can help in identifying potential insider threats.
Is there a way to track unusual activity in SCADA systems?
Yes, many IDS and IPS (Intrusion Prevention Systems) offer real-time monitoring features that can alert you to suspicious activities. Regularly update these systems for the best results.
Key Takeaways for Securing SCADA Systems
To wrap things up, always keep security at the forefront of your operations. Implement firewalls and intrusion detection systems effectively. Ensure your team is trained and aware of potential threats. Moreover, keep an eye on future trends and emerging technologies. Regular training and continuous monitoring are non-negotiable.
Honestly, I think the way forward is to be proactive rather than reactive. Regularly revisit your security protocols and keep striving for improvement. Your SCADA system is the backbone of your operations. Keep it secure, and you’ll sleep better at night.



If you’ve found these insights helpful, consider checking out more articles on industrialgyan.com for further tips and tricks. Until next time, stay secure!


I am an electrical & automation engineer with extensive experience in Design, PLC programming, SCADA development, and IoT integration. I have a strong background in the industry, focusing on the Design & Development of Hardware, Software &Industry 4.0 technologies, and the integration of intelligent manufacturing systems.
I have a deep understanding of electrical principles and am proficient in various programming languages, including Ladder Logic, Structured Text, and Python. In addition, I have experience with various PLC, SCADA & IoT technologies and a track record of successful integration projects for various clients.

